As part of our work on the DARPA Brandeis program, we developed backend server support for a particular implementation of Function Secret Sharing (FSS), which provides a real-time and scalable solution for privately collecting and storing user data. This technology has numerous applications – including fulfilling a crucial role in support of a concurrent DARPA program: Warfighter Analytics using Smartphones for Health (WASH). Namely, one of the performers on the WASH program (Kryptowire LLC, now Quokka) had developed mobile technology to detect when people were in close proximity to each other, a crucial functionality for contact tracing applications in public-health emergencies. Due to the sensitive nature of user location data, this information could (or at least should) not be collected and stored by a conventional central server – but storing real-time location data at scale in a privacy-preserving manner is a key strength of the FSS technology we had developed under the Brandeis program. Accordingly, in partnership with Kryptowire (and as part of a conjunction of the DARPA Brandeis and WASH programs), we developed a mobile application that privately collects user location data from mobile devices and stores it in a central location with strong privacy safeguards.
While location data is associated to each user, the server is unable to decipher any of the information it is holding, including which locations have people in them or whose data is being collected at any time. Meanwhile, when a user learns that they have become infected (e.g. with coronavirus), that user can (privately!) update all of their location data at the server, for example by adding an “infected” tag. Then as part of a regular “status check” (e.g. daily, or hourly), each user can probe the server to determine if they have recently (for example, within the past week) come into contact with an infected user – based on the (private!) timestamped locations the server is holding for every user.
Note that all information storage, update, and querying is accomplished privately, with strong guarantees on the server’s inability to learn sensitive information. In particular, all of the following information (user data and metadata) is completely hidden from the collecting server:
- Which user is accessing the system.
- What action the user is taking: Uploading (adding recent location information), Modifying (based on new infection status), or Probing (checking whether they have come into contact with another infected user).
- The result/output of the above action: which location(s) were updated, whether an infection status was updated (and what the current and prior statuses are), or the result of a probe.
- Aggregate information, for example density of users in a given location or the number of infected individuals.
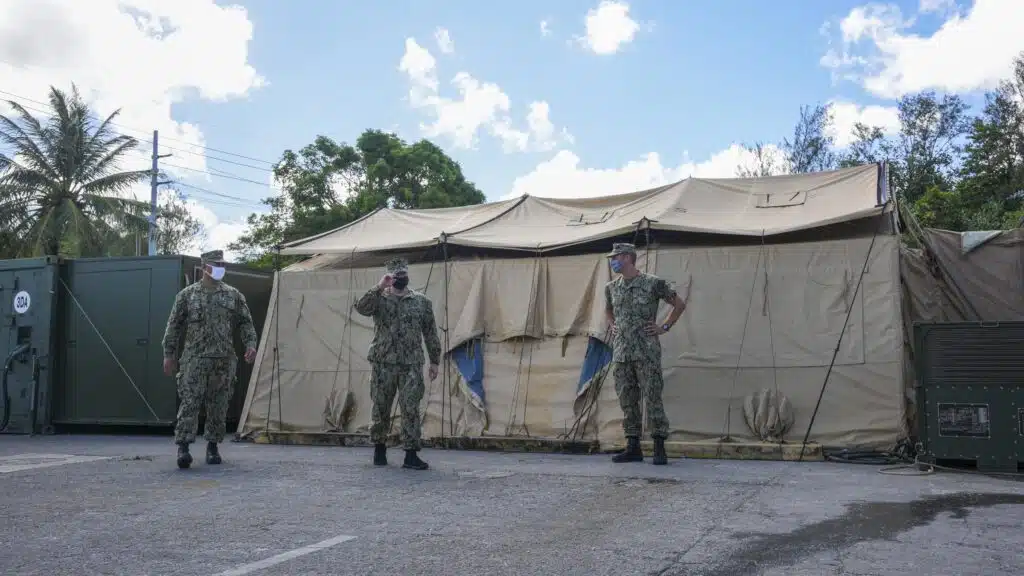
Our contact tracing prototype went through Independent Test & Evaluation (ITE) by Naval Information Warfare Center (NIWC) Pacific at the Naval Base Point Loma Topside. In this four-month experiment, we evaluated the smartphone application that we developed in collaboration with prime contractor Kryptowire, performing proximity tracking for COVID-19 contact tracing. The app leveraged GPS location to periodically determine proximity of users over the course of a month, and then reported this data back to a server hosting a privacy-protected database.
Objectives
The objectives of the experiment with NIWC Pacific were to evaluate the reliability, effectiveness, and utility of our software by testing it on a realistic dataset. Specifically, our dual objectives were (1) to evaluate the effectiveness of our smartphone application to perform proximity tracking of users on the naval base and (2) to evaluate the solution’s scalability as more data is collected within the system over time.
Outcome
The experiment was conducted between December 2021 and March 2022, and successfully demonstrated that our privacy-preserving database could handle the scale, activity, accuracy, and privacy objectives of the experiment.
This work was supported by DARPA and NIWC Pacific under Contract No. N66001-15-C-4065, Distribution Statement A: “Approved for Public Release, Distribution Unlimited. If you have any questions, please contact the Public Release Center”. The views, opinions and/or findings expressed are those of the author and should not be interpreted as representing the official views or policies of the Department of Defense or the U.S. Government.
