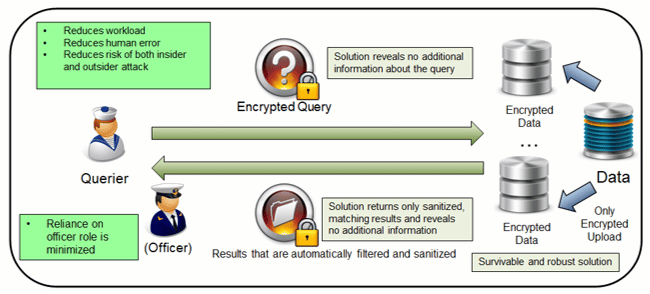
Downstream/Upstream Robust Automatic Secure Index Filtering Technology (DURASIFT) is a secure filtering technology that can streamline the way sensitive documents are stored and retrieved in an operational environment. This high-performance solution can be deployed to privately filter and redact information going both upstream and downstream, such that the filter terms are never revealed, the information flowing from the “high” to “low” side is properly sanitized, and the query terms can also be hidden. The goal of our project is to eliminate multiple potential points of inefficiency and insecurity, making it easier and more resilient against failures.
By automatically and securely reducing the amount of human interaction with sensitive data, our solution both increases workflow efficiency and decreases risk of sensitive information being mishandled. We envision three modes of operation, each suited for the correct situation:
- Queries from the low side are processed by the high side with appropriate filtering.
- Queries from the low side are securely processed by a “cloud” that operates on behalf of the high side. The guarantee is that the cloud never learns anything about the query or the filtering, even if it is penetrated by an adversary, and the low side never receives any sensitive information.
- Queries from the low side are securely processed by a physically outsourced “query box” (QB) that operates on behalf of the high side. The guarantee is that the box never learns anything about the query or filtering, even if it is captured by an adversary, and the low side never receives any sensitive information.
The technology is also applicable to coalition operations where sides need to cooperate towards a common objective without disclosing sensitive information to each other. Building DURASIFT required both developing the theoretical groundwork and practical implementations of secure filtering and cryptographic technologies, resulting in a scientific publication.
Our solution provides a multi-client, distributed database system that is both private and survivable against server outages, and furthermore allows clients to query a corpus of private documents and receive a sanitized response. The query and response are encrypted the entire time, hiding the documents, queries and policies from the servers executing the query, and hiding the policies and redacted documents from the client. Our scheme is built using a combination of secure multiparty computation (MPC) and private information retrieval (PIR), but is highly optimized to be efficient for real-world use on moderate sized databases of unstructured, tagged text documents. The system supports multiple owners (who can upload documents and set access policies), multiple clients (who can make queries), and multiple servers who execute the queries.
Work done under ONR Contract N00014-16-C-1032. DISTRIBUTION STATEMENT A: Approved for Public Release, Distribution Unlimited.
